Three-factor authentication is the new two-factor authentication
Two-factor authentication continues to provide our online selves with more security for our email and online banking. Meanwhile, in the physical world, protecting our valuables is now all about three-factor authentication.

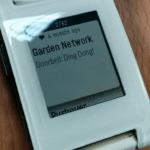
Not sure what I mean? Here’s a video from Switched On Network that demonstrates how to use a Raspberry Pi to build a three-factor door lock comprised of an RFID keyring, 6-digit passcode, and one-time access code sent to your mobile phone.
Note that this is a fairly long video, so feel free to skip it for now and read my rather snazzy tl;dr. You can come back to the video later, with a cup of tea and 20 minutes to spare. It’ll be worth it, I promise.
The tl;dr of three-factor door locks by Alex Bate
To build Switched On Network’s three-factor door lock, you need to source a Raspberry Pi 3, a USB RFID reader and fob, a touchscreen, a electronic door strike, and a relay switch. You also need a few other extras, such as a power supply and a glue gun.

Once you’ve installed the appropriate drivers (if necessary) for your screen, and rotated the display by 90 degrees, you can skip ahead a few steps by installing the Python script from Switched On Network’s GitHub repo! Cheers!
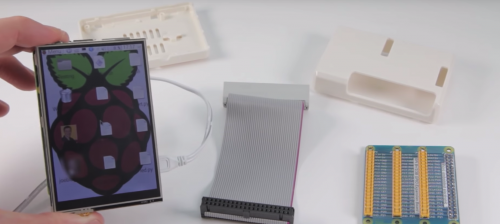
Then for the physical build: you need to attach the door strike, leads, and whatnot to the Pi — and all that together to the door and door frame. Again, I won’t go into the details, since that’s where the video excels.

The end result is a superior door lock that requires you to remember both your keys and your phone in order to open it. And while we’d never suggest using this tech to secure your house from the outside, it’s a perfect setup for inside doors to offices or basement lairs.

Everyone should have a lair.
Now go watch the video!




10 comments
Mr A Non
In the security sector, e.g. PCI, three factor authentication requires three *different* factors. Common factor definitions are “something you know” (e.g. password, but can be easily shared), “something you have” (e.g. mobile phone/RFID tag), and “something you are” (e.g. a biometric). So, in this example, a one-time-password sent to your phone would still be a “something you have”, same as the RFID tag, so still classed as two-factor authentication. For a deeper discussion on this, see https://pciguru.wordpress.com/2010/05/01/one-two-and-three-factor-authentication/
Ignoring my pedantry, looks a really interesting project – both for the overall concept, and for giving starting points for people wanting to deal with the individual elements of RFID reading, sending one-time-passwords etc (although just saw they’re storing plaintext PINs/passwords in a database, which is never a good thing – Troy Hunt has a good article on password (or PIN) storage https://www.troyhunt.com/everything-you-ever-wanted-to-know/).
Cordial
This was my exact thought when reading the article. Interesting concept, but I don’t think this is considered 3-factor authentication. I’m also not sure that it brings much more security gain than a traditional 2FA solution, so I see it more as marketing for the project rather than a contribution to security.
Fox Keegan
I thought the same, but was just amused there’s a gif of a fingerprint scanner on the page, when that’s the aspect that’s missing.
Noel
This isn’t three factor authentication, just three inputs of two security factors. When we speak of multiple factors in security, we are referring to the four authentication factors: something you have (device or keyfob), something you know (password or pin), something you are (biometrics), and somewhere you are (used much less, but used for things like identifying if the device is connected to its home network).
This implementation features something you know, the passcode, and two instances of something you have, the keyfob and phone. While it might be arguably marginally more secure to require two things that have to be stolen in order to access the system, the actual security complexity this sort of setup adds does not amount to much. Additionally, the one time passcode delivery systems on the market are typically not very secure. SMS messages in particular are notoriously easy to intercept and should never be used over time-based authenticators like Google authenticator.
Studies have shown that users find actual three-factor authentication less burdensome than multiple implementations of two factors. For some reason, our brains just accept it more. You would be better off implementing a cheap fingerprint reader or IR camera into this setup both for greater security and better user acceptance.
AndrewS
“it’s a perfect setup for inside doors to offices or basement lairs.”
…or for guarding your precious cookie / oreo stash ;-)
https://www.raspberrypi.org/blog/laser-cookies/
Fox Keegan
Speaking as someone with a background in InfoSec, that’s pretty cool. Nice to see one-time-use codes coming within the realm of everyday folks.
OTOH, speaking as someone with a background in InfoSec, I have to recommend to everyone: before you go to this effort, realize that physical security is a large domain of information security–neat, high-tech security is impressive, until a common criminal gets around it like he would any other lock by kicking in your door.
Lengthy explanation you can probably skip:
The video very specifically says internal doors, but let’s use a hypothetical one everyone can imagine: Your home’s front door. Understand that your front door probably swings into your home, like nearly every other front door out there. That’s because that keeps your hingest inside, so they can’t be tampered with. But you’ll notice most businesses have doors that swing outward. This is generally because egress laws require it. (In the event of a fire the door has to swing the way people would be running away, cuz bad things have happened otherwise.) This means they have hinges on the outside. That’s bad for them, right? Not anymore; we have tamper-resistant hinges now. It actually provides them with a very specific benefit that most homeowners don’t get: trying to kick in a door that swings outward requires the attacker to break through the door jamb–the extended part of the door frame that stops a door when it closes shut. By contrast, on the door to your home, it’s being kicked in the direction it swings, so it doesn’t need to go through the jamb. So rather than a chunk of wood attached to the frame (and wall) the length of the door, the only thing the attacker needs to break is the little bit of frame with the mortise for the strike plate and latch bolt. The strike plate are generally held in place by tiny screws, and the wood stopping the whole thing from being kicked inward is perhaps an inch wide. It’s literally a simple matter of splitting off a bit of wood.
So while high tech is super cool, if it’s important enough to protect it with three factors of authentication, it’s probably also important enough to ensure you’ve more than an inch of wood, or two sheets of 5/8ths inch drywall separating your valuables from an attacker. Make sure the door either swings towards you, or there’s a big servo moving a metal bar across the back of the door. Or both. With a steel door. And reinforced walls. :)
Zak Zebrowski
Looking at the video, a fire warden would condemn the building. Personnel safety in the event of fire always has to trump security. The solution above doesn’t satisfy the need of having a panic bar / emergency exit button to exit the room, overriding the security system. $0.02
MehWhoCares
You’re assuming I don’t want the people that are attempting to steal my belongings to burn in a fire. Sometimes safety during a fire is less important. ?
zook
Wrong implementation, for physical access is should be, one thing with you have, one with you are, one with you know. For example rifd card, password and fingerprint.
You have two with you have and one with you know.
Roger Z
Yet, all it takes is just a nice and shiny crowbar. ;)
Comments are closed