Homemade anti-tracking device
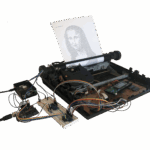
Matt Edmondson is a digital forensics expert and federal agent with the Department of Homeland Security, and he created a Raspberry Pi-based anti-tracking tool after a friend got worried they were being followed. No, he won’t say who the friend is. Matt is terrible at sharing gossip, which makes him a very good federal agent.

What is it made of?
The entire device fits inside a waterproof case the size of a shoebox. A Raspberry Pi 3 runs the software while a Wi-Fi card and wireless signal detectors look for nearby devices. A portable charger powers everything, and a touchscreen shares each alert the device sends so the user gets a visual indication of which devices keep popping up and how often.
How does it work?
The device runs Kismet software to detect smartphones and tablets nearby that are looking for Wi-Fi or trying to connect to Bluetooth devices. Kismet is a network detector, packet sniffer, and intrusion detection system, and it runs with any wireless card that supports raw monitoring mode.
We all know our phones track our app usage and location, but you may not be aware that your phone is also constantly looking for wireless networks around it. And it gets especially excited when it finds a network it has connected to before. “Especially excited” is the technical term for “doing something different which notifies Kismet in a special and different way”. If Kismet finds a device that it has seen in the last twenty minutes, it flashes up a warning to let the user know they might be being tracked.

Matt wrote code in Python to keep lists of the devices that his anti-tracking tool has come into contact with, so that the software can check its log and see the last time it came across each device.
This homemade tracking device is designed for use on the move. If you’re sitting for a long time in one place where lots of other people are also hanging around for longer periods, like a cinema or a restaurant, you’ll get pinged every twenty minutes to let you know your seat neighbours might be tracking you.
You can see Matt’s presentation on this device to last month’s Black Hat USA security conference, or head to GitHub to take a look at his code for this anti-tracking build.


9 comments
Matt
Could you add a link to the project? Thanks
Raspberry Pi Staff Helen Lynn
Rats – we obviously dropped that on the floor somewhere along the way. Added; thanks!
Bonzadog
28.9.2022
An excellent article and idea.
I would like more details about the HW used, if possible.
beta-tester
not really new, some shops using this method to track customer/visitors in their shops (via WiFi, BT, GSM). so i don’t think serious “agents” have their mobilephones WiFi or BT turned on.
some smartphone OS versions have an option to randomize its MAC for every search for networks nearby – at least for WiFi search.
how practical is this box? if you don’t have a backpack where you can store it, it is not small enough to keep it with you all the time – ok, in some countries you use you car nearly for everything – but not here where i am.
i hope this box does not radiate any signature itself – otherwise you could get tracked even easier … :P
Paul
In terms of portability and stealth, this whole project can be accomplished using a smartphone with NetHunter OS installed. You wouldn’t even need an external WiFi dongle if you have a phone that has kernel monitor mode support. Can’t get much more portable and stealth than a regular looking smartphone.
Clayton Ross
Add in a few sdr dongles and sweep more bands and I would be impressed
Serge Khachatour
This is an awesome article. Thanks for sharing. I have to try this out :) i have all the hardware and can expand on this with a a few nodejs servers. WOW possibilities are endless!
Cheers!
exlibris
It can also be interesting for home security, detecting the same Wi-Fi nearby can warn of thieves watching.
Sakura
Stored information should be geo-tagged. This avoids false alarms when standing still. But above all, it allows alarming if the same device is detected near us in various places. It would be more practical to use the geo tag instead of the time tag.
Comments are closed